Is Buying Through AI at Work Cyber Safe?

Artificial intelligence is already embedded in many workplaces. Tools such as Microsoft Copilot and ChatGPT now help teams write emails, summarise documents, and answer questions quickly. However, the next stage of AI adoption is moving beyond productivity. Increasingly, these tools are starting to support buying through AI at work. This development introduces a new question for […]
Multi Factor Authentication in Businesses Is No Longer Optional

Passwords were once the main line of defence for business systems. However, cyber criminals have become far more sophisticated. As a result, organisations that rely on passwords alone now face a much higher level of risk. A recent cyber security investigation uncovered a large scale data theft campaign that affected dozens of organisations around […]
Preparing Your Business for Modern Cyber Threats
Modern cyber threats are no longer about random disruption or noisy attacks that shut systems down without warning. Instead, cyber criminals are becoming more strategic, more organised, and far more precise in how they target businesses. They now focus on quiet access, long term presence, and maximum leverage. While that may sound worrying, […]
Fake App Malware Threats on the Rise

Fake App Malware Is Becoming a Serious Threat Why Businesses Need To Stay Alert When you download a new app for work, how sure are you that it is the genuine version? This question matters more than ever, especially as fake app malware continues to grow at an alarming rate. Cyber criminals are […]
AI Powered Cyber Attacks Now Make Up 80% of Malware Threats.
The Rise of AI Powered Cyber Attacks Why Small and Medium Businesses Need to Act Now What if I told you that AI powered cyber attacks are more common than attacks planned or carried out by people. This is the reality that businesses now face. Recent research shows that 80 percent of ransomware […]
Cybersecurity Concerns: FBI Issues New Ransomware Warning
The FBI Has Issued a Warning About a New Ransomware Threat: Interlock Don’t be made victim to new business cybersecurity concerns. Be aware and be prepared. When was the last time you stopped to think, “What would actually happen to my business if all our files were suddenly locked away?” That is exactly the nightmare […]
Is Your Smart Office a Security Risk? What Small Businesses Need to Know About IoT

Is Your Smart Office a Security Risk? What Small Businesses Need to Know About IoT Your office thermostat, conference room speaker, and smart badge reader are convenient, but they’re also doors into your network. With more devices than ever in play, keeping track can be tough, and it only takes one weak link to put […]
Securing Your Supply Chain: Practical Cybersecurity Steps for Small Businesses

Securing Your Supply Chain: Practical Cybersecurity Steps for Small Businesses Picture this: your business’s front door is locked tight, alarm systems are humming, and firewalls are up, but someone sneaks in through the back door, via a trusted vendor. Sound like a nightmare? It’s happening more often than you think. Cybercriminals aren’t always hacking directly […]
Decoding Cyber Insurance: What Policies Really Cover (and What They Don’t)

Decoding Cyber Insurance: What Policies Really Cover (and What They Don’t) For small businesses navigating an increasingly digital world, cyber threats aren’t just an abstract worry, they’re a daily reality. Whether it’s phishing scams, ransomware attacks, or accidental data leaks, the financial and reputational damage can be severe. That’s why more companies are turning to […]
A Small Business Guide to Implementing Multi-Factor Authentication (MFA)
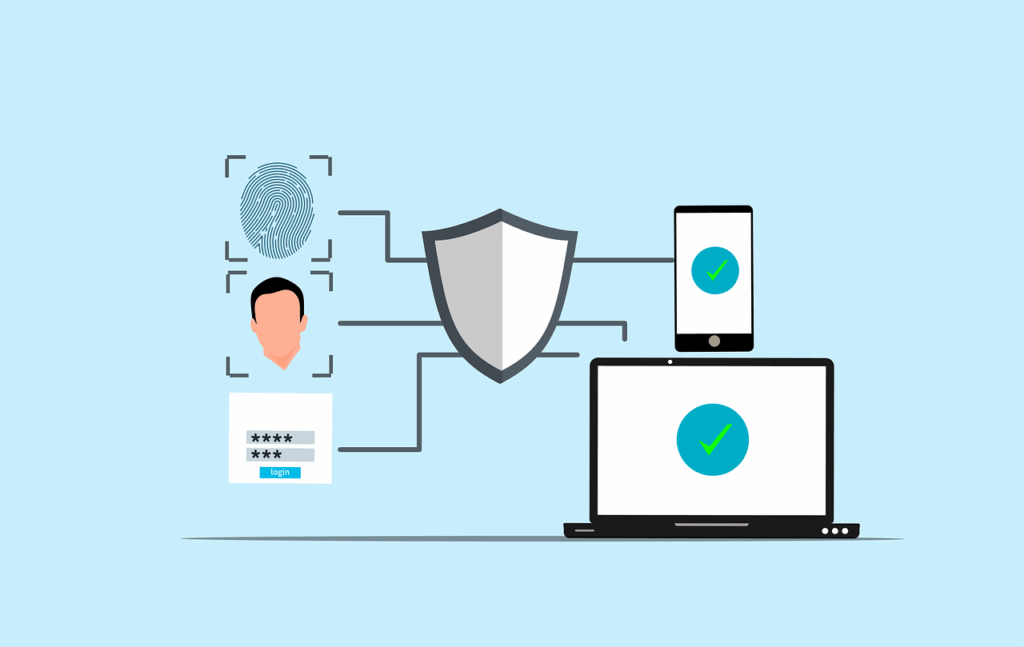
A Small Business Guide to Implementing Multi-Factor Authentication (MFA) Have you ever wondered how vulnerable your business is to cyberattacks? According to recent reports, nearly 43% of cyberattacks target small businesses, often exploiting weak security measures. One of the most overlooked yet highly effective ways to protect your company is through Multi-Factor Authentication (MFA). This […]
