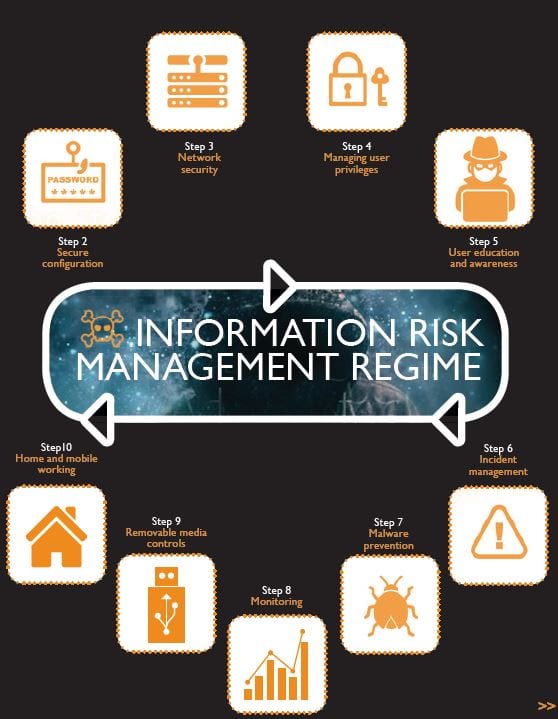
Information Risk – 10 Steps to Cyber Security
The Information Risk Management Regime, is central to an organisations’ overall strategy to manage and control the threat of Cyber-attacks. Surrounding and supporting this regime are 9 additional steps, collectively, providing the basis for a secure cyber environment.
Cyber-attacks continue daily. The scale of these attacks show little signs of abating. As born out in the latest Cyber Security survey – How Businesses are Faring This guidance is for businesses looking to protect themselves in cyberspace.
Following the 10 steps to cyber security below, your business will be ready to gain accreditation through the Cyber Essentials scheme.
Your Managed Service Provider will have knowledge and expertise to guide you.
10 Steps to Cyber Security
 Information Risk Management Regime
Information Risk Management Regime
Assess the risks to your organisation’s information assets with the same vigour, as you would for legal, regulatory, financial and operational risks. Embed an Information Risk Management Regime across your organisation and an empowered Information Assurance (IA) structure. Communicate your Risk Management Policy to employees, contractors and suppliers. This is so that they are aware of your organisation’s risk management boundaries.
 Secure configuration
Secure configuration
Manage the configuration and use of your systems by developing secure baseline builds and introducing corporate policies and processes. Remove or disable any unwanted functionality from systems, keeping them patched against known vulnerabilities. Failure to do this will expose your business to threats and vulnerabilities. This would increase the risk to confidentiality, integrity and availability of systems and information.
 Network security
Network security
Connecting to un-trusted networks (such as the Internet) could expose your organisation to cyber-attacks. Configure perimeter and internal network segments. Follow recognised network design principles. Monitor traffic for unusual or malicious incoming and outgoing activity.
 Managing User privileges
Managing User privileges
Provide Users with the privileges that is required for their role only. Control the number of privileged accounts for roles such as system or database administrators. Ensure this type of account is not used for high risk or day-to-day user activities. Monitor User activity, particularly all access to sensitive information and privileged account actions, such as creating new user accounts, changes to user passwords and deletion of accounts and audit logs).
 User education and awareness
User education and awareness
User security policies, describing acceptable and secure use of your organisations systems. Train Users regularly on the cyber risks they face as employees and individuals. Security related roles such as system administrators, incident management team members and forensic investigators will require specialist training.
 Incident Management
Incident Management
Establish an incident response and disaster recovery capability that addresses the full range of incidents that may occur. Testing on a regular basis the following:
- Incident management plans
- Disaster recovery
- Business continuity too.
Your incident response team may need specialist training across a range of technical and non-technical areas. Report online crimes to the relevant law enforcement agency. This will help the UK to build a clear view of the national threat.
 Malware prevention
Malware prevention
Produce policies that directly address the business processes such as the following:
- web browsing
- removable media
- personal devices that are vulnerable to malware.
Scan for malware across your organisation and protect all host and client machines with antivirus solutions that will actively scan for malware. Scan information supplied to or from your organisation for malicious content.
 Monitoring
Monitoring
Establish a monitoring strategy and develop supporting policies. Consider previous security incidents and attacks, and your organisation’s incident management policies. Continuously monitor inbound and outbound network traffic to identify unusual activity or trends that could indicate attacks and the compromise of data. Monitor all ICT systems using Network and Host Intrusion Detection Systems (NIDS/HIDS) and Prevention Systems (NIPS/HIDS).

Removable media controls
Produce removable media policies that control the use of removable media for the import and export of information. If the use of removable media is unavoidable, then limit the types of media that can be used together with the Users, systems, and types of information that can be transferred. Check for malware before any data is imported to your organisation’s system.
 Home and mobile working
Home and mobile working
Assess the risks to all types of mobile working. Include remote workers, where their device connects to the corporate network infrastructure. Develop appropriate security policies. Train mobile Users on the secure use of their mobile devices for locations they will be working from. Apply the secure baseline build to all types of mobile device used. Protect data-at-rest using encryption (if the device supports it) and protect data-in-transit using an appropriately configured Virtual Private Network (VPN).
